Beini gives you the same tools that hackers use to test your wireless network and patch security holes, making your home network more secure from the inside out. The first thing you’ll notice is that this is a very light and fast Linux distribution – you’ll be able to run it off a small 100MB USB key (we suggest having more space free. Use handshake packets to crack WPA/WPA2 password. For cracking WPA/WPA2 password, we will use tool named aircrack-ng. Aircrack-ng will unpack the handshake packet and will match the wordlist passwords one by one with the handshake packet. There are multiple ways to crack WPA/WPA2 passwords using wordlist attack.
WiFi Password Hacking Software
WiFi Cracko is the application developed in purpose to find password to access protected WPA/WEP, WPA2 & WPA3 network security types.
Internet users who are not so highly educated about digital networking or computing in general usually have problems of recovering back their WiFi (WLAN) password in case they've forgot it. This often happens after changing a router and forgetting to save a new password to a safe place.
This is why the WiFi Cracko tool is created - To help people hack into their router quickly and get their password in only few minutes!
The software is supported to work on multiple operating systems & devices.
OS Supported:
- Desktop: Microsoft Windows, MacOS
- Smartphone: Android .APK, iPhone/iPad with iOS
Click the button below to go to the files page where you can download the tool.
User Instructions:
WiFi Cracko is created with a very user friendly interface so even beginners can easily understand how to operate with it. Here is a step by step guide how to hack to hack WiFi password using our tool.
Step #1 - Download the app on your device and install it.
Step #2 - Click the 'Scan for Available Networks' button and wait a moment until all SSID available networks are listed in a box below.
Note: Hacking mobile hostspot of iPhone or Android phones is also possible since they have their own WLAN system built in.
Step #3 - Select the one you've decided to hack. Recommended is one with strongest signal.
Step #4 - Check its security type WEP/ WPA/ WPA2-PSK/ WPA3). If you are not sure, click the 'How do I know this' link and the tool will automatically check this for you.
Step #5 - Click 'Start Hacking' button and wait until the tool cracks a password. Time will depend on how strong is password made. If it's made of mixed characters, numbers, uppercase & lowercase letters etc. then it may take up to half an hour to crack a password successfully. But usually users are waiting around 3 to 5 minutes.
Step #6 - Done! Enjoy browsing the internet again!
Crack Wpa2 Beini Free Fire
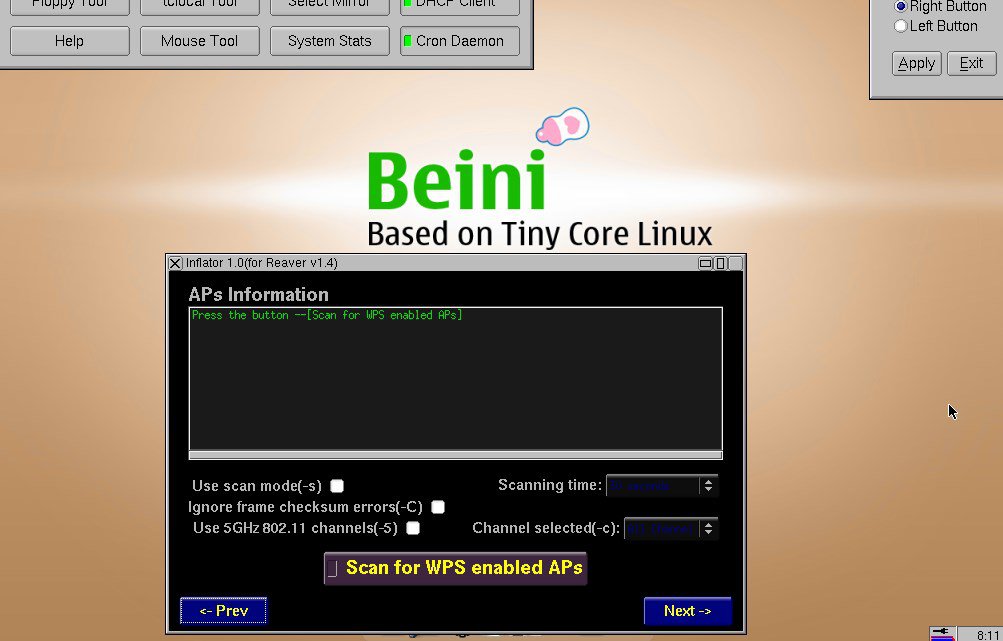
Choose WPA/WPA2, choose scan time (recommend 5 minutes or above). Step by step to crack WiFi password using Beini Feeding Bottle (1) Step by step to crack WiFi password using Beini Minidwep-gtk (1) Followers. Online Casino In Australia Posh bingo Roulette hits counter BWIN BONUS. How to Hack WEP WPA WPA2 Networks with Beini YouTube Abdirahman Ahmed. Capture and Crack WPA Handshake using. Como Hackear redes Wifi Wpa Wpa2-Psk!! Con Beini 1.2.5 y Diccionarios!
| Open in a new tab to enlarge this image |
3. If you were successful to boot up then you should see something likethis. Click Minidwep-gtk.
5. Now Minipwep-gtkprogram will open. Click Scan.
8. If it found a password, it should appear like this.
See also:
How To Turn A Laptop or Desktop Into A WiFi Hotspot Easily!
How to Hack any Email account passwords easily!
Crack Wpa2 Beini Free Trial
How Do You Detect If Someone are Stealing Your WiFi!
How To Hack Wi-Fi Using Linux Backtrack!
Updated Users are urged to continue using WPA2 pending the availability of a fix, experts have said, after security researchers went public with more information about a serious flaw in the wireless encryption protocol.
So-called Key Reinstallation Attacks, aka KRACK, potentially work against all modern protected Wi-Fi networks. Depending on the network configuration and the device targeted, it is possible to inject and manipulate data as well as eavesdrop on communications over the air. The only main limitation is that an attacker needs to be within range of a victim to exploit these weaknesses.
It affects WPA2 Personal and Enterprise, regardless of the encryption ciphers used by a network. It mostly affects Linux and Android 6.0 and above, as well as macOS and OpenBSD. Windows and iOS are more or less unaffected due to the way they implement WPA2. Gadgets from Cisco, Linksys and other networking gear makers are also vulnerable. You should obtain and install software patches as soon as possible, from your operating system vendor or hardware suppliers, to fix up the WPA2 design flaw.
Mathy Vanhoef of KU Leuven, one of the security researchers who discovered the specification blunder, warned that the security hole stems from a fundamental cryptographic weakness in the latest generation of wireless networking rather than a programming cockup.
Simply changing Wi-Fi network passwords is not going to help – software and firmware will need to be updated to workaround this deep design error:
The weaknesses are in the Wi-Fi standard itself, and not in individual products or implementations. Therefore, any correct implementation of WPA2 is likely affected. To prevent the attack, users must update affected products as soon as security updates become available.
KRACK targets the four-way handshake of the WPA2 protocol and relies on tricking a victim's device into reusing an already-in-use key. This sleight of hand is achieved by manipulating and replaying cryptographic handshake messages.
WPA2 security in trouble as KRACK Belgian boffins tease key reinstallation bug
READ MORE“When the victim reinstalls the key, associated parameters such as the incremental transmit packet number (i.e. nonce) and receive packet number (i.e. replay counter) are reset to their initial value,” Vanhoef explained today on a microsite about the attack. “Essentially, to guarantee security, a key should only be installed and used once. Unfortunately, we found this is not guaranteed by the WPA2 protocol. By manipulating cryptographic handshakes, we can abuse this weakness in practice.”
An attacker can force these nonce resets by collecting and replaying retransmissions of message three of the four-way handshake.
A nonce is a number that is not necessarily a secret but is meant only to be used once and never repeated. The flaw in WPA2 allows a nonce to be – or forced to be – repeated, thus allowing an attacker to extract the WPA2 session key and decrypt and compromise all wireless traffic for that session.
As a proof-of-concept, Vanhoef has published a demonstration of how a key reinstallation attack might be carried out against an Android smartphone. Android and Linux are particularly susceptible to the WPA2 flaw because a bug in the platform's widely used wpa_supplicant tool zeroes the key during the eavesdropping, thus the Wi-Fi traffic can be trivially decrypted.
In short, other than Windows and iOS, the vulnerability can be exploited on various operating systems, computers and devices to decrypt any information transferred over the air that isn't already encrypted with HTTPS, TLS, a VPN tunnel, or similar.
Worse, there's a bug in wpa_supplicant that causes the key to be set to all zeroes when you do this attack, so all traffic is trivially decrypted when attacking Linux and Android clients.
— Graham Spookyland 🎃 (@gsuberland) October 16, 2017Users are urged to continue using WPA2 pending the availability of a fix. VPN and other security technologies can offer protection to connections pending the availability of software update, according to preliminary analysis by one security researcher.
Crypto expert Arnold KL Yau told El Reg: “This sounds bad. However, a significant amount of the risk would be mitigated for services that use strong encryption at the transport or application layer (such as TLS, HTTPS, SSH, PGP) as well as applications secured by encrypted VPN protocols.
'Despite this, however, the ability to decrypt Wi-Fi traffic could still reveal unique device identifiers (MAC addresses) and massive amounts of metadata (websites visited, traffic timing, patterns, amount of data exchanged etc.) which may well violate the privacy of the users on the network and provide valuable intelligence to whoever's sitting in the black van.”
Research behind the attack will be presented at the Computer and Communications Security (CCS) conference in November, and at the Black Hat Europe conference in December. A technical paper titled Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2 is available here. Frank Piessens of imec-DistriNet, who supervised his research, is credited as joint author of the paper.
Previous research by Vanhoef in related areas of HTTPS and Wi-Fi security can be found here and here.
Crack Wpa2 Beini Free Download
Computers and modern phones are easy to patch, but it's the embedded devices and Internet-of-Things gizmos that are tricky to upgrade to address the WPA2 flaw.
Mark James, a security specialist at ESET, told us: “One of the biggest concerns here of course is getting routers patched - firstly getting the average user to check and apply any firmware updates and secondly, some older routers may not even have a patch available - the average household would acquire an auto-configured router, install it and forget about it, until possibly they change their internet provider. Here, they may go through the same procedure; too many people never check or implement router updates as it’s something often too complicated for the home user to be involved in.”
Crack Wpa2 Beini Free Version
This guide will tell you How To Solve Sun Dial Puzzle In Assassins Creed Origins so that you can finish the Final Fantasy XV cross-over event, complete the quest and obtain the special Final Fantasy cross-over items. This puzzle is part of the A Gift from the Gods side quest. Assassin's creed origins sundial puzzle answers.
Below is a video by Vanhoef demonstrating the wireless security weakness in Linux and Android. ®
Updated to add
Check out this follow-up article for details on patches and caveats to KRACK.
Sponsored: How the CLOUD Act affects your company's data